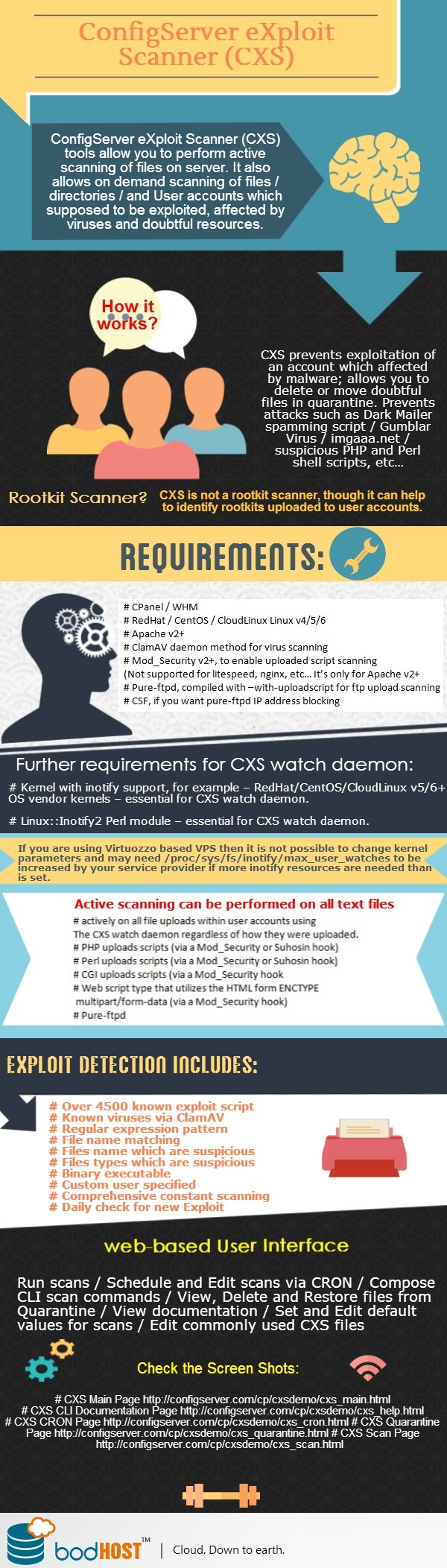
With the assistance of ConfigServer eXploit Scanner (in short CXS) tool you can perform active scanning of files which uploaded to the server. This tool also allows to execute on demand scanning of files/directories / and the user accounts that supposed to be exploited, viruses, and doubtful resources. You can scan existing users’ data to check if there any exploits have been uploaded in the past or through methods that not covered by the active scanning. This tool is specifically made to increase server performance and scalability.
CXS prevents exploitation of an account which affected by malware; allows you to delete or move doubtful files in quarantine. Prevents attacks such as Dark Mailer spamming script / Gumblar Virus / imgaaa.net / suspicious PHP and Perl shell scripts, etc…
Active scanning can assist to prevent the exploitation of an account that affected by malware; you can delete or can move suspicious files to quarantine before they become active. This also includes exploits such as Dark Mailer spamming script (multiple variants, including complicated code regardless of the file name) and files uploaded with the Gumblar Virus, also the imgaaa.net defacement scripts.
It also block the uploading of suspicious PHP and Perl shell scripts, which commonly used to launch more malicious attacks and for sending spam.
Remember, CXS is not a rootkit scanner, though it can help to identify rootkits uploaded to user accounts.
Requirements:
# CPanel / WHM
# RedHat / CentOS / CloudLinux Linux v4/5/6
# Apache v2+
# ClamAV daemon method for virus scanning
# Mod_Security v2+, to enable uploaded script scanning
(Not supported for litespeed, nginx, etc… It’s only for Apache v2+
# Pure-ftpd, compiled with –with-uploadscript for ftp upload scanning
# CSF, if you want pure-ftpd IP address blocking
Further requirements for CXS watch daemon:
# Kernel with inotify support, for example – RedHat/CentOS/CloudLinux v5/6+ OS vendor kernels – essential for CXS watch daemon.
# Linux::Inotify2 Perl module – essential for CXS watch daemon.
Remember, if you are using Virtuozzo based VPS then not possible to change kernel parameters and may need /proc/sys/fs/inotify/max_user_watches to be increased by your service provider if more inotify resources needed than set.
Active scanning can be performed on all text files:
# actively on all file uploads within user accounts using the CXS watch daemon regardless of how they were uploaded.
# PHP uploads scripts (via a Mod_Security or Suhosin hook)
# Perl uploads scripts (via a Mod_Security or Suhosin hook)
# CGI uploads scripts (via a Mod_Security hook
# Web script type that utilizes the HTML form ENCTYPE multipart/form-data (via a Mod_Security hook)
# Pure-ftpd
Exploit detection includes:
# Over 4500 known exploit script fingerprint matches (in addition to ClamAV detection)
# Known viruses via ClamAV
# Regular expression pattern matching to help identify unknown exploits
# Filename matching
# files name which are suspicious
# Files types which are suspicious
# Binary executable
# Custom user specified regular expression patterns
# Comprehensive constant scanning of all user data using the CXS Watch daemon – scans all user files as soon as they modified
# Daily check for new Exploit Fingerprints … and more!
Included with the CXS Command Line Interface (CLI) is a web-based User Interface (UI) to help:
# Run scans
# Schedule and Edit scans via CRON
# compose CLI scan commands
# View, Delete and Restore files from Quarantine
# View documentation
# Set and Edit default values for scans
# Edit commonly used CXS files
Check the Screen Shots:
# CXS Main Page http://configserver.com/cp/cxsdemo/cxs_main.html
# CXS CLI Documentation Page http://configserver.com/cp/cxsdemo/cxs_help.html
# CXS CRON Page http://configserver.com/cp/cxsdemo/cxs_cron.html
# CXS Quarantine Page http://configserver.com/cp/cxsdemo/cxs_quarantine.html
# CXS Scan Page http://configserver.com/cp/cxsdemo/cxs_scan.html