
Today, we are going to see how to install “Maldet” on CentOS. Remember, ConfigServer eXploit Scanner (CXS) and Maldet plays an important role in the sever security.
Installation steps for Linux Malware Virus Scanner:
To install the Maldet on a specific source path:
#cd /usr/local/src/
First, download the tar file of Maldet using the following URL:
#wget http://www.rfxn.com/downloads/maldetect-current.tar.gz
To extract the file use the below command:
#tar -xzf maldetect-current.tar.gz
To enter the Maldet folder use:
#cd maldetect-*
Now, run the below command to install Maldet:
#sh ./install.sh or sudo sh ./install.sh
It will show the below output:
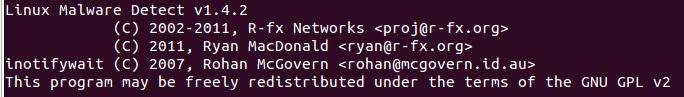
The installation will be complete in /usr/local/maldetect
Config file: /usr/local/maldetect/conf.maldet
Exec file: /usr/local/maldetect/maldet
Exec link: /usr/local/sbin/maldet
Cron.daily: /etc/cron.daily/maldet
Maldet (32517): {signup} performing signature update check…
Maldet (32517): {signup} local signature set is version 2010051510029
Maldet (32517): {signup} latest signature set already installed
To perform the update task use the following commands:
#maldet –update-ver
#maldet –update [/i]
To perform scanning task for the files:
#maldet –a/home/username/
It will scan all the files and will provide the output:
To scan all users under public_html folder under /home*/ this can be done with:
#root@server~] #maldet –scan-all /home? /? /public_html
To scan the same path but the content that has been created or modified in the last 5 days:
#root@server[~]# maldet –scan-recent /home?/?/public_html 5
If you forget to turn on the quarantine option, then you can quarantine all malware results from a previous scan with:
#root@server[~]# maldet –quarantine SCANID
If you want to clean all malware results from a previous scan that did not have the feature enabled, then you can do this
#root@server[~]# maldet –clean SCANID
If you had a file that was quarantined from a false positive or that you simply want to restore (i.e.: you manually cleaned it), you can use the following:
# root@server[~]# maldet –restore config.php.2384
# root@server[~]# maldet –restore /usr/local/maldetect/quarantine/config.php.2384